Duke NetID Login Page Gets New look
Security update to also require multi-factor authentication for more web sites
Quincy Garbutt recently sent a message to Duke’s IT Security Office when he saw something online that looked suspicious.
"I reported it as suspicious because I wanted to thwart any chances of this propagating and affecting others on campus," said Garbutt, an IT Analyst with Trinity Technology Services supporting the Provost Office.
This is exactly the type of behavior that security officials hope students, faculty, and staff will take when they see something unfamiliar with a website seeking their NetID and password.
That’s why the IT Security Office is giving advance notice about a change in design for Duke’s standard NetID login page that will go into effect July 5.
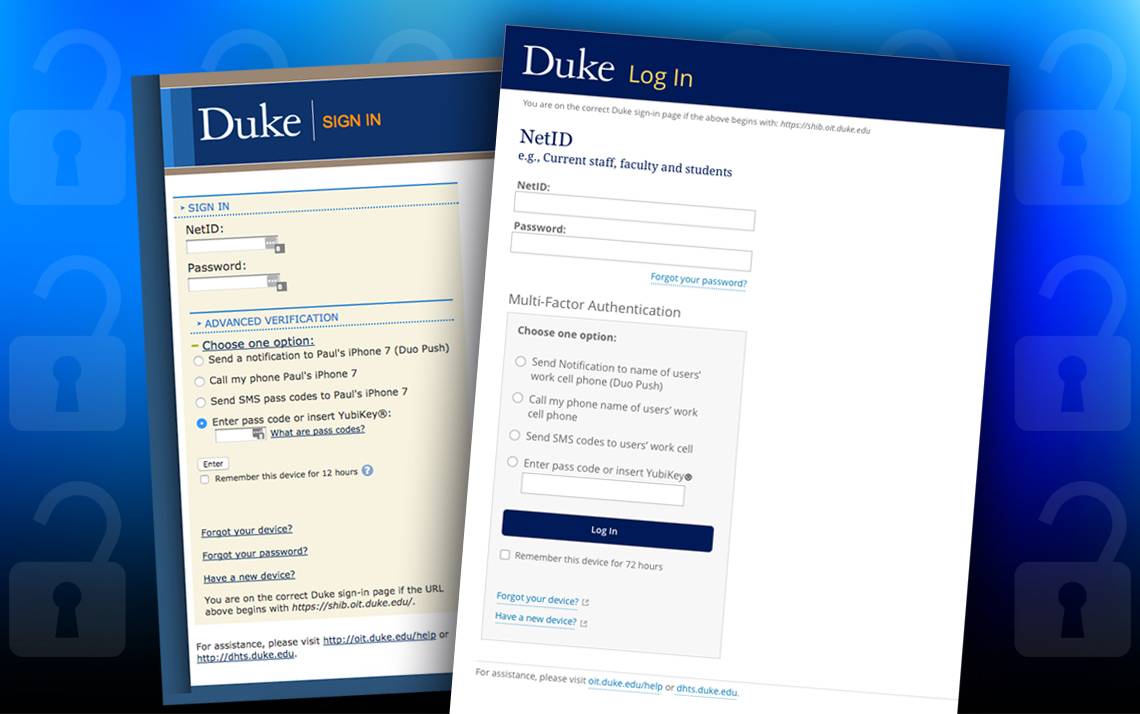
New Login Look
After the Fourth of July holiday, members of the Duke community will find a newly designed NetID login page when accessing protected content on Duke-affiliated websites.
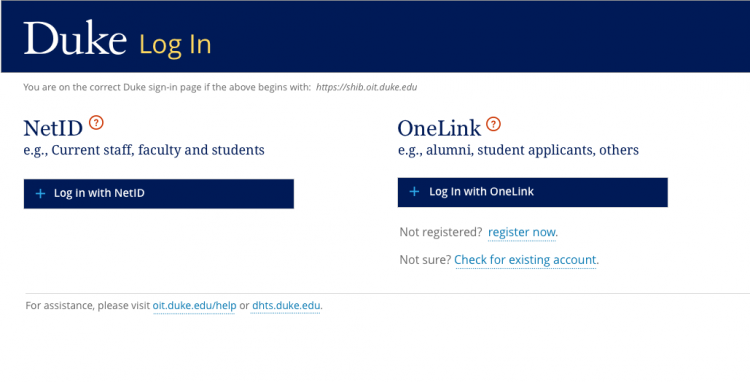
The login’s new look and feel is being updated to be consistent with Duke’s online branding style, but does not change its function. Users will continue to use their NetID and password to access secure websites and resources.
Users may also see an alternative login option called “OneLink” on select sites. OneLink is a Duke account for those who do not have a NetID, such as alumni or student applicants. Faculty and staff should always use their NetID login.
Adding Multi-factor Authentication
The login page redesign is paired with increased security for three key sites. Duke already requires multi-factor authentication (MFA) for Duke@Work. MFA requires a NetID and password, plus a second form of verification, such as a code or approval sent to a mobile phone.
As of July 5, MFA is being extended to three additional services that potentially house sensitive data. MFA will be required for staff and faculty, only when they are off Duke's network (e.g. at home, or while traveling) for:
- Box (box.duke.edu)
- Sakai (sakai.duke.edu)
MFA will be required for staff and faculty both on and off the Duke network for:
- DukeHub (formerly known as ACES/Storm or Peoplesoft)
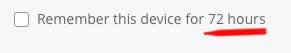
A key enhancement to the MFA process is an increase in the length of time the MFA verification is active – from 12 hours to 72 hours. This will allow users to login with MFA just one time during that period from the same web browser.
 Later this year, MFA will be required for two additional services – Duke’s Office 365 webmail service (mail.duke.edu) and the campus Virtual Private Network (VPN) service (portal.duke.edu.) The intent is to protect these accounts from attackers who might use compromised email accounts to send phishing messages or to use a compromised VPN account to access Duke resources improperly.
Later this year, MFA will be required for two additional services – Duke’s Office 365 webmail service (mail.duke.edu) and the campus Virtual Private Network (VPN) service (portal.duke.edu.) The intent is to protect these accounts from attackers who might use compromised email accounts to send phishing messages or to use a compromised VPN account to access Duke resources improperly.
“We continue to see strong evidence that attackers focus their efforts on obtaining user accounts whether to send spam from compromised email accounts, or to access sensitive data. Multi-factor authentication is one of the best ways to protect Duke, and our faculty and staff accounts," said Chief Information Security Officer Richard Biever. “We selected these sites for two reasons – first to protect any sensitive data they may contain, and second to protect services that could be vulnerable to account takeovers that result in increased phishing attacks or illegitimate access to Duke services.”
Duke users may add MFA anytime to these and other Duke sites by visiting https://oit.duke.edu/mfa.
If Duke users need assistance setting up MFA or have questions about the new login page, please contact the OIT Service Desk at oit.duke.edu/help or for hands-on help visit the Link in the lower level of Perkins Library.